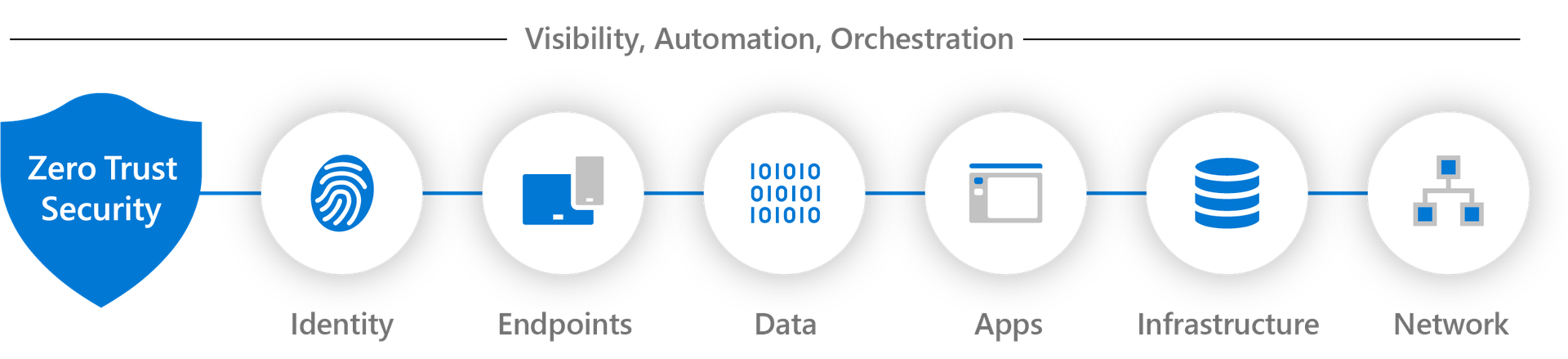
In this blog post, we propose a roadmap to progressively strengthen your Zero Trust posture in Microsoft 365, based on Microsoft’s Zero Trust model and its seven technology pillars: Identity, Endpoints, Applications, Data, Network, Infrastructure, and Visibility, Automation, and Orchestration. Rather than attempting to implement all controls at once, this approach breaks the journey into clear, manageable steps, each building on the trust signals and enforcement capabilities introduced in the previous stage.
On a monthly basis, we will publish a dedicated blog post that explores one aspect of Zero Trust in Microsoft 365 in depth, aligned with one or more of these pillars. Each article focuses on practical technical implementation, architectural decisions, and concrete configuration examples, helping organizations move from Zero Trust principles to enforceable and measurable security controls.
Together, these articles form a structured learning path designed to guide organizations from foundational identity and access enforcement to a mature Zero Trust operating model that integrates detection, response, automation, and continuous improvement across the Microsoft 365 platform.
Microsoft 365 Zero Trust Roadmap 2026
Identity as the Primary Enforcement Point
How to ensure that all access to Microsoft 365 is evaluated and enforced through Microsoft Entra ID by establishing strong authentication and a clean identity foundation, including hybrid identities.
Identity Risk and Protection
How to use Entra ID Protection for risk-based Conditional Access in Microsoft 365, and use Microsoft Defender for Identity to monitor and investigate on-premises identity risk in hybrid setups.
Devices as Trust Signals
How to use device compliance and endpoint risk signals to restrict cloud access to Microsoft 365 resources using Conditional Access.
Application Context
How to apply different access requirements depending on the application being accessed by using authentication context, application sensitivity, and session controls.
Network and Location Context
How to incorporate network and location information into access decisions while avoiding assumptions of trust based solely on IP addresses or network placement.
Conditional Access Architecture
How to understand Conditional Access evaluation logic and design a clear policy structure that consistently evaluates identity, device, application, and network signals.
Conditional Access Policy Design
How to structure Conditional Access policies so they remain readable, predictable, and manageable as environments grow and requirements evolve.
Data Protection
How to apply data classification, labelling, and data loss prevention controls so that security decisions continue to matter after authentication.
Detection, Response, and Automation
How to detect trust violations across identities, devices, and sessions and automate response actions using Microsoft 365 Defender and Microsoft Sentinel.
Operating Zero Trust
How to monitor Conditional Access effectiveness, review policy impact, and adjust controls as users, devices, and threats change.
User Experience and Access Friction
How to measure and reduce unnecessary authentication prompts and access issues while maintaining the required level of security.
Zero Trust Maturity
How to assess Zero Trust maturity using practical metrics and continuously improve security controls across all seven Zero Trust pillars.
Congrats!
You completed the Microsoft 365 Zero Trust Roadmap.